February 12, 2026
Imagine a scenario where you receive a phone call from your boss. Their request is urgent, they need you to quickly wire them some money to secure a new vendor contract. You know the sound of your boss’s voice, so there is little to bring you any sense of alarm, and even if there was, would you say “no” to your boss? And yet, it’s not actually your boss, it’s a cybercriminal using AI to clone your boss’s voice to fool you. This may sound like a scene from a sci-fi thriller but it’s the reality we face in our ever-advancing age of AI and cybercrime.
We are well-educated on how to spot suspicious emails by keeping an eye out for poor grammar, misspelled words, and unusual attachments. But we have not had to train on how to question the voices of people we know. This makes AI voice cloning exploitation (also known as “vishing”) especially likely to happen. Cybercriminals only need brief seconds of audio found online through news interviews, social media posts, or presentations to replicate someone’s voice. With just a small sample they can use AI tools to use the voice to say anything they type. This makes for this type of attack incredibly easy to pull off because not much technical skill is needed on the part of the attacker, and what they can produce is highly convincing.
This is a recipe for disaster, especially if the exploitation comes in the form of what seems to be a boss or person in leadership. Most employees are trained to do as they’re asked to and not question what sounds like a genuine person in authority. Criminals use this to their advantage and will often stage these attacks just before a weekend or holiday to increase the pressure on the employee to comply with the request being made without taking the time to verify. In addition to all this, AI technology can even generate a variety of emotions and inflections with their sample voice, producing the sound of anger, frustration, or fatigue. This is a form of emotional manipulation on the employee that is getting vished and can interrupt logical thinking.
Spotting a fake email from a hacker is much easier than detecting a fake voice. Unfortunately, there aren’t many tools that currently exist to expose deep fakes. Despite that, there are some things you can look for to spot a fake. Pay attention to see if the voice sounds slightly robotic, unusual breathing patterns, strange background noises, or odd cues or phrases in how they greet you. Though this isn’t the most reliable approach for detection, it can still be helpful until the technology improves to help protect you.
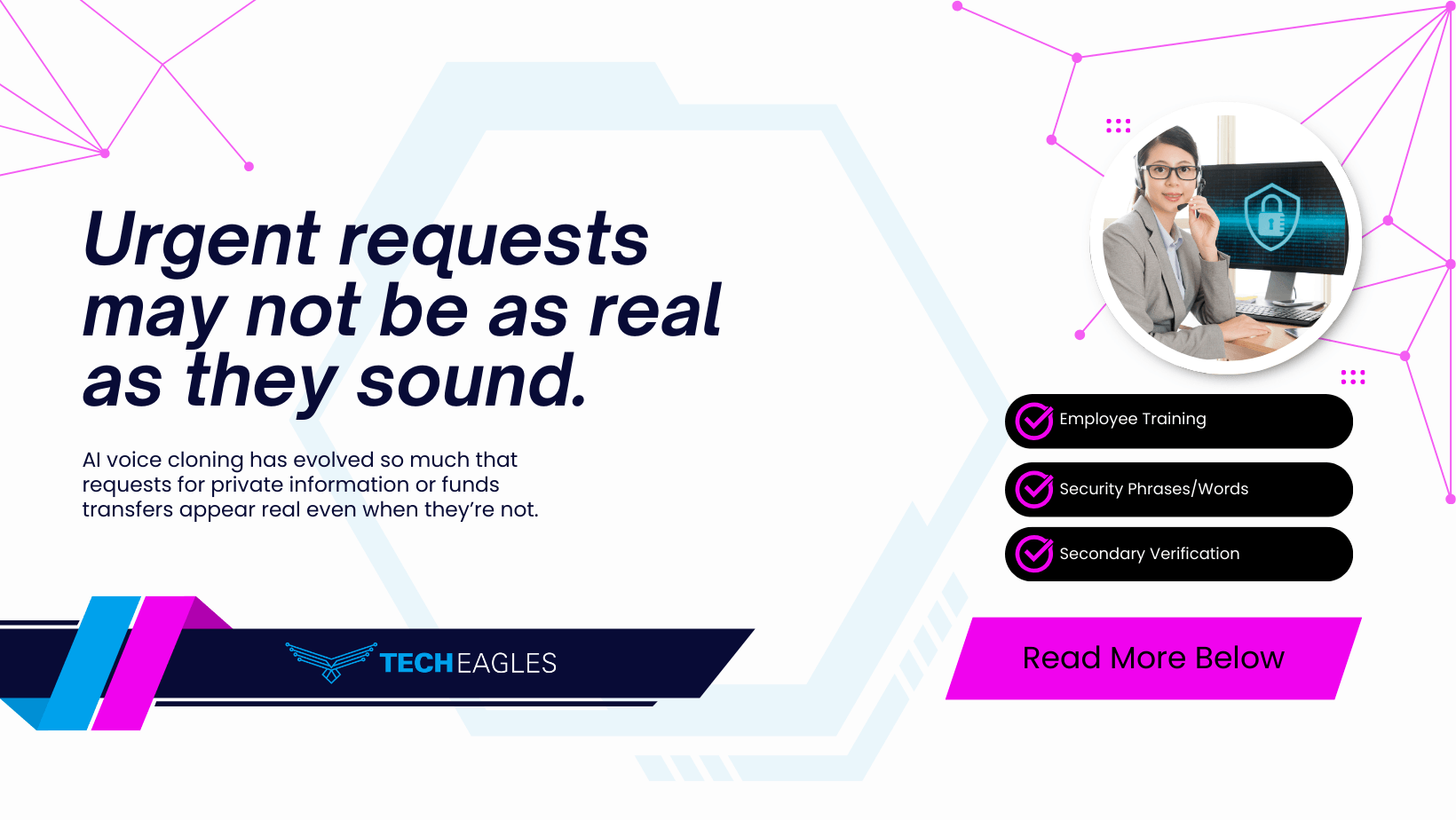
This makes cybersecurity training for employees even more important. Be sure to educate your team on these very real AI threats along with your standard best practices. Make the reminder of it a regular habit. You can even incorporate vishing simulations to see how your employees respond under pressures. Additionally, having a “zero trust” policy for voice-based requests involving money or data can be protocol for your team, requiring verification through a secondary channel for all such requests. This can easily be done when a person in leadership calls an employee for a money or data request, the employee can hang up the phone, then call that leader back on their internal line or send them an encrypted message through apps like Teams or Slack to confirm the request. Some businesses are now going so far as to establish “code words” or “safe words” that are known only by specific employees. So, if a caller does not provide or respond to the secret word or phrase, the request can be declined and all is well.
As AI technology evolves, so must our awareness and caution in the workplace. Waiting until an incident occurs will likely mean that it’s too late to protect your business from an attack. Tech Eagles can help secure your data, build a fortress around your business tech, ensure that you are compliant with federal and state industry standards, and provide cybersecurity training for your team. Give us a call today.
